Single sign-on (SSO) is an authentication scheme that allows users to access to multiple, independent software systems with one set of login credentials. SSO can be used by enterprise organizations as well as smaller businesses and individuals to sign into programs and applications more easily without memorizing dozens of passwords.
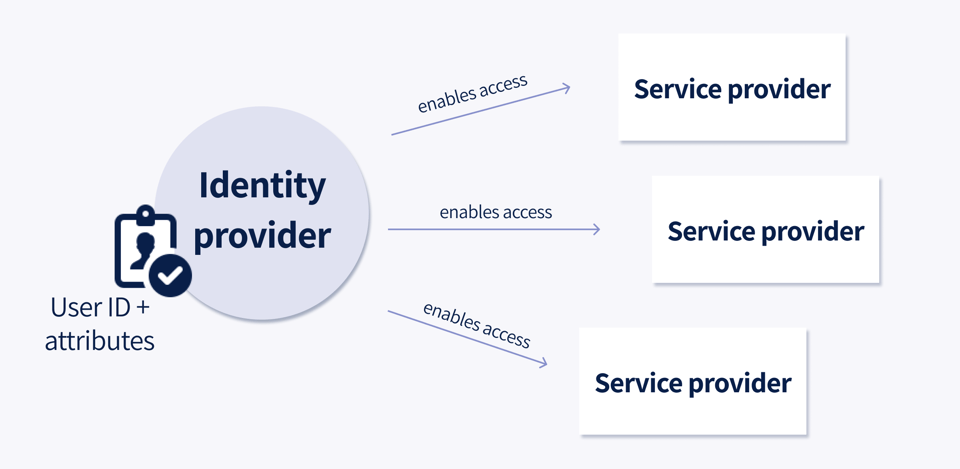
With a traditional SSO setup, there is usually an identity provider and a service provider.
The identity provider (IDP) acts as the source of truth for your user information. It stores a user’s ID and attributing information and enables users to access third-party services – the service providers – without exposing passwords.
The service provider (SP) verifies a user’s identity to provide access to the application without needing to create another set of login credentials.
When configuring SSO, the IDP and the SP agree on the user attribute that will be used as the user/unique identifier. When a user authenticates to the IDP, the IDP creates a SAML assertion that contains user information and authentication data. The SP uses this information to verify the user.
For a deeper dive into SSO, check out this comprehensive video.
Identity providers and service providers must work together to set up authentications and ensure security for end users. One example of a common SSO configuration is using Google as an identity provider in order to access several service provider applications including YouTube and Glassdoor.
.png?width=1108&name=Picture1%201%20(1).png)
Notice how the Glassdoor website allows users to login using their Google or Facebook credentials. Google and Facebook are considered identity providers and Glassdoor is a service provider application in this example.
Should my organization implement an SSO strategy?
Many businesses that implement SSO do so for the benefit of their employees. With SSO, employees do not need to remember and securely track multiple usernames and passwords. Because logging into platforms is easier, employees are more likely to utilize company-provided resources. SSO also lessens the chance of phishing and decreases password management requests to IT teams.
Benefits of an SSO strategy:
- Easier password management
- Lower barrier to enter company-provided resources
- Lower chances of phishing
- Decrease in password management requests to IT teams
That said, there can be associated costs with setting up SSO. To implement an SSO connection between two applications that haven’t connected before, it is necessary for both parties to work together on the configuration requirements. Be sure to clarify the scope of the SSO strategy among your providers to ensure a smooth implementation.
How does SSO work with Konverse?
Konverse can act as both an identity provider and a service provider application in SSO setups depending on the needs of your organization.
Konverse as the identity provider: Konverse supports multiple service providers today, and continuously collaborates with partners and their 3rd party vendors. With Konverse as your identity provider, it acts as the centralized workplace where employees start and end their days. This setup is dependent on other apps agreeing to SSO authentication scheme in collaboration with Konverse.
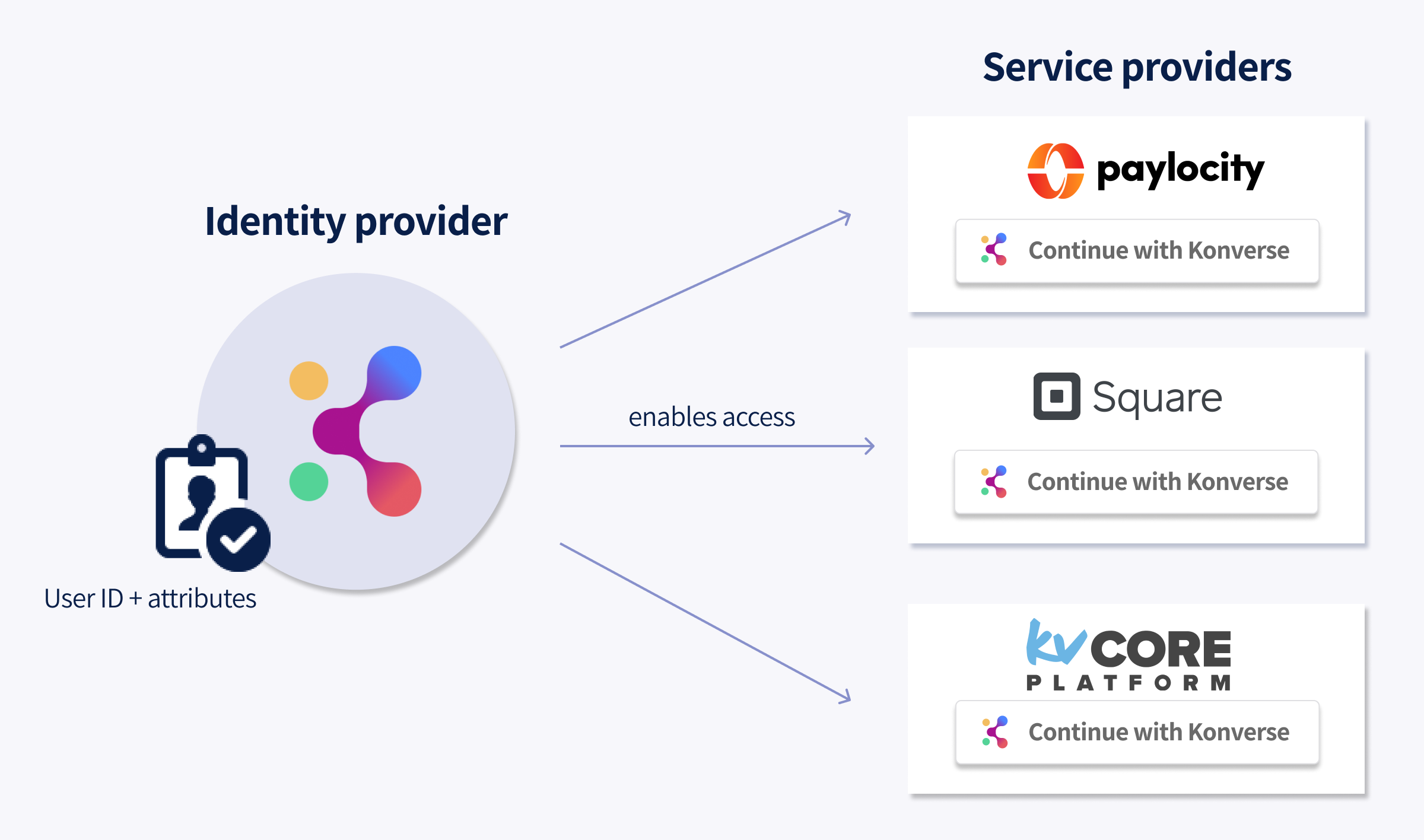
A simplified view of Konverse as an identity provider.
Konverse as a service provider: Connect Konverse with major identity providers such as Okta, OneLogin, Google Workplace, or MS Azure. Users will easily log in to the Konverse app using their company identity provider. This low-effort approach makes accessing Konverse easier for employees.
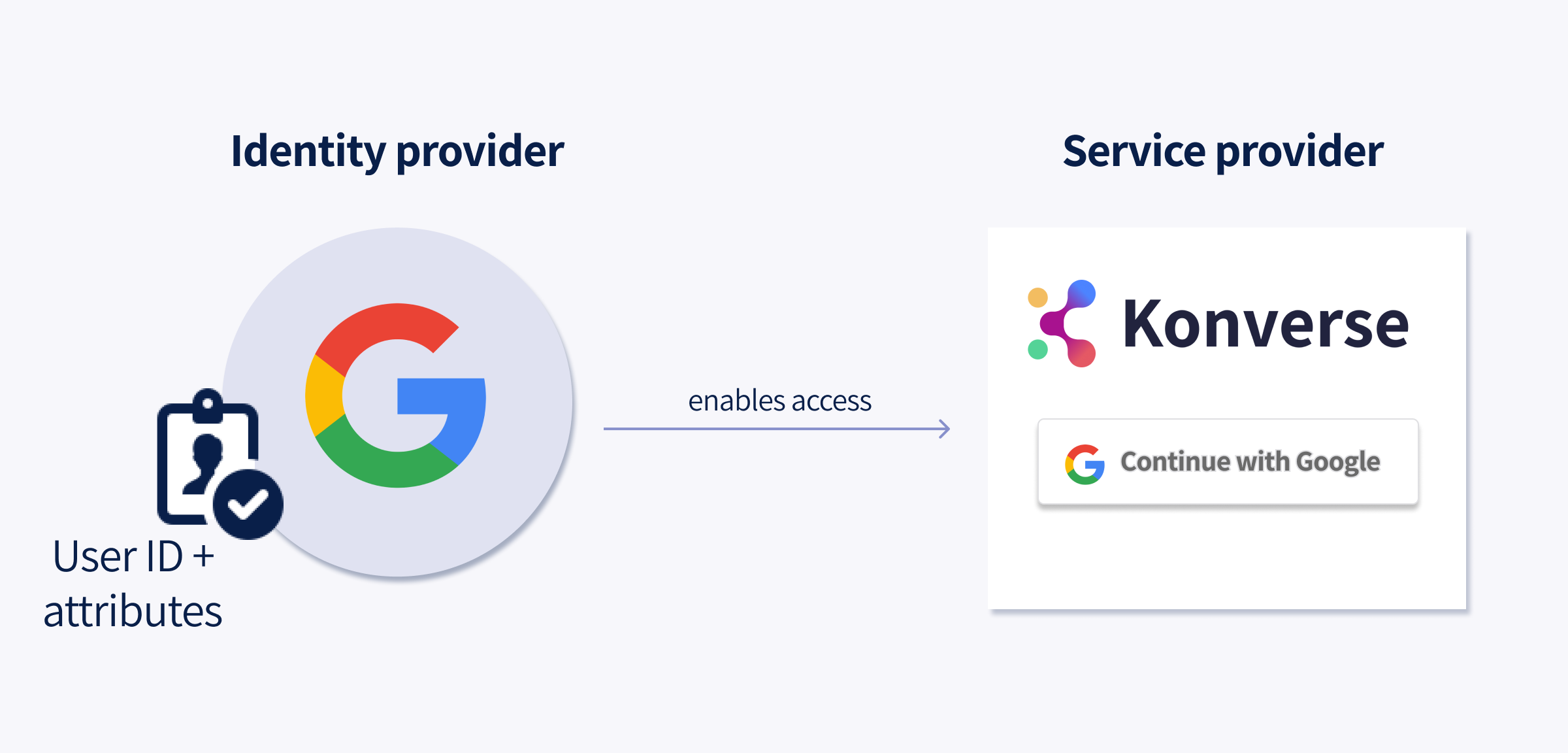 A simplified view of Konverse as a service provider.
A simplified view of Konverse as a service provider.
Setting up SSO with Konverse
There are many reasons an organization may want to invest in SSO, from simplifying sign-on to improving technology adoption. If you’re interested in an SSO implementation with Konverse, contact us.